TriOp update - version 1.4 (and Shodan Trends)
· ☕ 1 min read
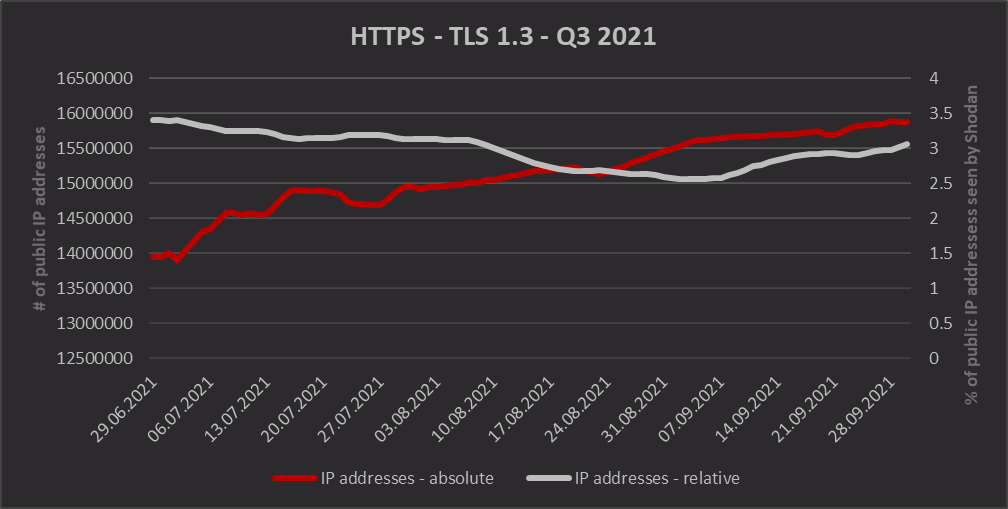
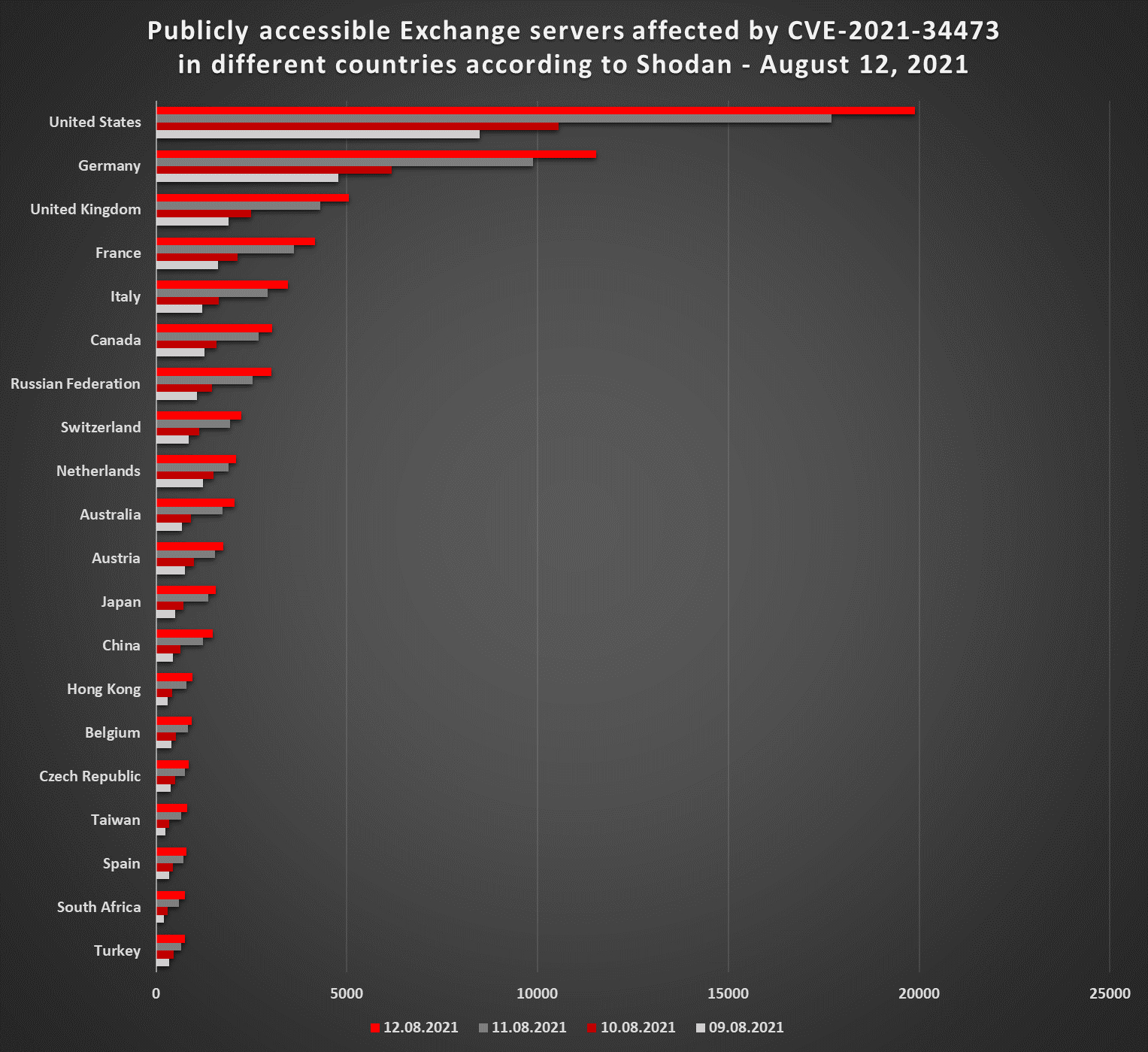
I’ve published version 1.4 of TriOp today. The only change in this version is the addition of CVE-2021-31206 (vulnerability used in the ProxyShell attack) to the relevant search list. One additional point that deserves a mention is that Shodan has recently opened access to a new service called Shodan Trends...